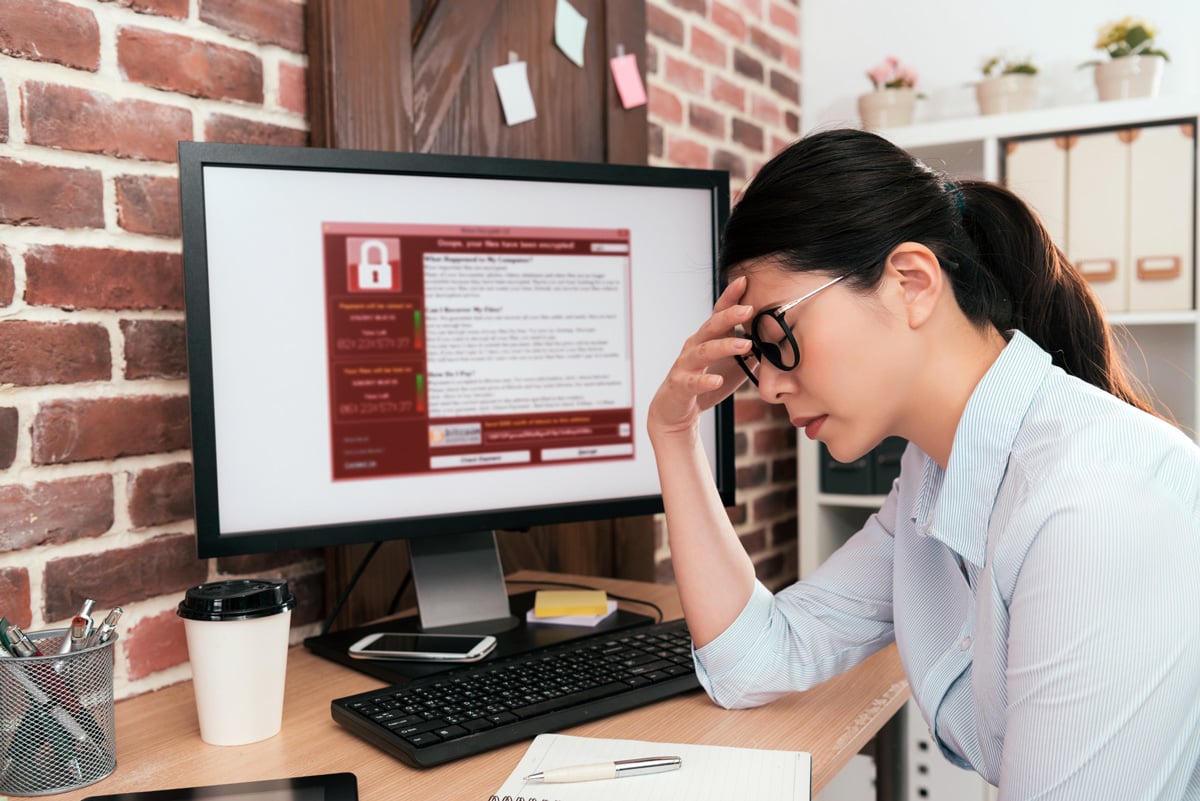
 When you think of risks to your workplace, you may think of terrorists, extreme weather events, fire or theft.
When you think of risks to your workplace, you may think of terrorists, extreme weather events, fire or theft.
A far more likely threat is actually your team...
"If you don’t bake cybersecurity into your engagements, you do yourself and your customers a disservice" - James Khan, Managing Director of Idea 11 (AWS-specialist Managed Service Provider).
Cybersecurity is a team sport
Whether it’s complacency, laziness or an ignorance of how serious the risks are and how we’re exploited, the majority cause of serious cybersecurity breaches has been confirmed to be the users in your team.
Telstra’s most recent report reveals that in 2019 65% of Australian businesses have reported data breaches, a 5% increase from 2018.
The need to be vigilant and thorough in protecting your data and organisation from harm has never been greater.
“It’s IT’s job to protect us”
A common belief exposed from cybersecurity investigations is that employees believe that it’s up to their Information Technology department to protect them and their organisation from technology-based harm.
The truth is far more complex, of course.
In Cisco’s annual report on 2018, research indicated that only 26% of all cybersecurity threats can be protected by equipment and software alone. The remaining 74% required user training, policy and procedure or combinations of these elements.
Balancing the human element
Cyberhackers returned to social engineering as their long-preferred attack method in 2018, after flirting with cryptomining and exploits in 2017. They have re-affirmed that we the users, remain the weakest link in the cybersecurity fabric.
Weak passwords and opening suspicious emails remain as key problems for IT Managers. These problem stem directly from fellow employees, but originate from the conflicting demands of cybersecurity and productivity.
Read our blog on: Why your password isn't good enough
To eliminate most of our cybersecurity risk is possible, but unpalatable, as it severely restricts our access to data and functionality that is vital for us to be productive.
Obviously, tilting the scales towards productivity too far leaves us very vulnerable to cybersecurity risks.
Cybersecurity is a constant “cat and mouse game”, with defenders continually racing to adapt to existing threats while trying to prevent future threats. The most stable flaw for attackers to exploit is the people, as we fail to improve our processes to assist the hardware, software, and policies that protect us.
Cybersecurity is often described using the analogy of an “onion”, each layer playing its part in providing protection. User training and cybersecurity awareness remain an important layer of that protection, along with the technological and operational resources used to protect our data integrity.
Five tips on protecting your data
Consider these tips in improving your cybersecurity defences:
1. User training
Training for all levels of users on cybersecurity awareness raises people’s vigilance on what to look for to spot a cybersecurity threat. Training will also improve an employee’s response to a threat – we have seen client’s employees turn off their computer and leave for a long weekend after knowingly infecting their local area network.
Data breaches are now an event that has requirements for mandatory reporting under Australian Law.
(See the Office of Australian Information Commissioner website)
2. Policy and procedure
Policies and procedures should include disaster recovery and backup/restore of data, password complexity, mandatory reporting of breaches, cybersecurity training, multi-factor authentication and much more.
Policies need to be defined and regularly updated to provide the right balance between security and productivity for your workplace. There needs to be an open dialog between end-users and IT management about how their productivity is affected by limited access, and in reverse how security is reduced by increased access.
3. Use multi-factor authentication
We are stuck with passwords for a while yet.
Passwords are near the end of their usefulness, now that password complexity requirements are exceeding our ability to create and remember effective passwords in our day-to-day work life.
There are ways we can extend the usefulness and reduce the demands of passwords while still improving security.
A good example is multi-factor authentication (MFA), usually implemented as two factor authentication (2FA).
2FA is the practice of having users require a second method of authentication beyond their password, such as biometrics (fingerprint, iris scan, facial recognition) or an SMS or smartphone-based app.
Multi-factor authentication is one of the most effective methods of improving the authentication of users, and it can be implemented in a way that provides a minimum of impact on productivity.
4. Password managers
PC and smartphone users may already be familiar with password manager programs.
Password managers are typically a digital lockbox that holds a database of login credentials for other resources. Password managers also assist in creating very complex passwords and storing them for the users, eliminating the need to remember these difficult credentials.
Read our guide on: Why your password isn't good enough
5. Don't forget about mobile
Smartphones and any other "Bring Your Own" Device (BYOD) are a source of threat to every organisation. This is due to their unpredictability in the rapid change of technology, and the fact that these devices are exposed to threats in multiple environments, outside of the influence and control of your corporate network.
As users utilise their BYOD devices as another work space to use with their corporate accounts, they increase the risk of cross-infection between systems. If phones are used as 2FA devices, this increases the risk to corporate systems.
Read more on: Mobile threat detection
Cybersecurity is everybody’s responsibility
Management need to set and regularly review policies and procedures regarding access, authentication and authorisation for users at all levels.
IT departments need to set and regularly review access rights with users to ensure they’re getting their best possible productivity with the minimum access to provide a balance between cybersecurity and productivity.
Cybersecurity training for all levels of employees is every bit as important as the other means of protection, including software, hardware and security practices in keeping our data (and jobs!) safe.
Improve your business security
Diamond IT's Business Technology Managers (BTMs) are experts in the holistic transition from legacy IT and policies/procedures into a modern, integrated system with "baked-in" security.
Contact us on 1300 307 907 and select Option 1 for our Sales department to start your move into a safer work environment or contact us online below.




